How to Rethink ThirdParty Access BankInfoSecurity
Third-party access refers to the process of an organization granting external vendors and service providers secure access to corporate IT assets for maintenance, administration and management purposes. Many organizations rely on third-party vendors and managed service providers to support their internal IT systems, applications and.
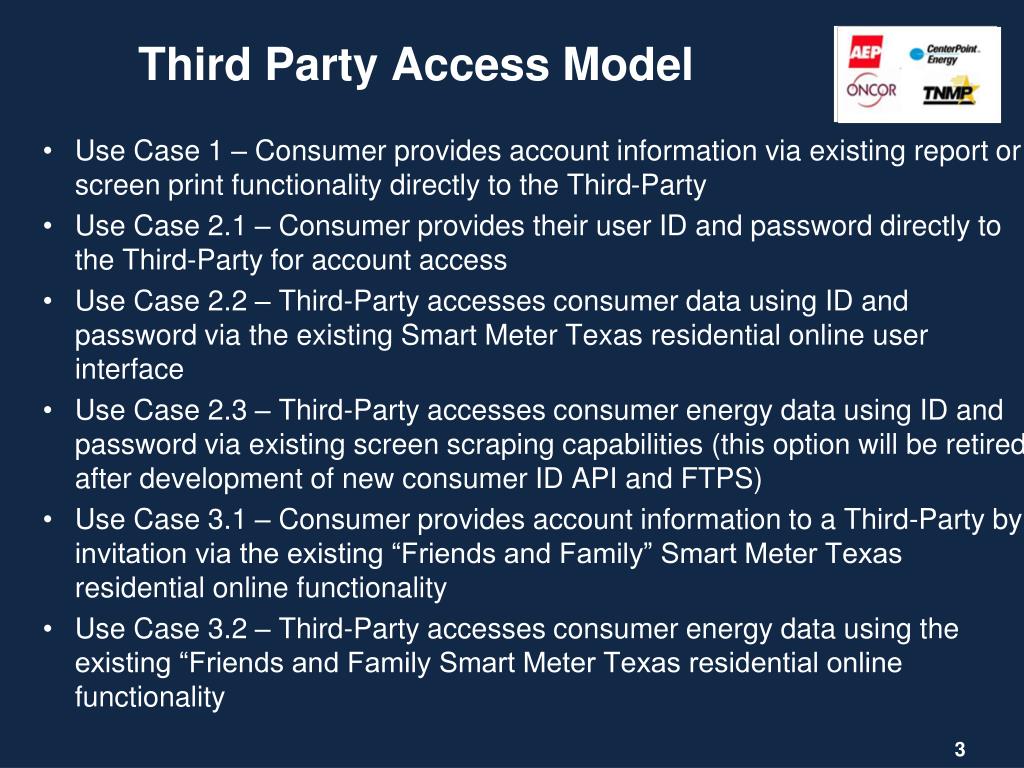
PPT SMT Model for Third Party Access PowerPoint Presentation, free download ID5503852
Third-party access governance can increase security, reduce the chances of data breaches and other cyberattacks, and deliver significant cost savings. By preventing data breaches, organizations can avoid the vast amounts of money involved in data recovery, legal fees, and reputation damage.

ThirdParty Access Governance Features Saviynt
Understand & Assess Vendor Access Risk. Contractors, HVAC companies, building maintenance, consultants, suppliers, contingent staff, IT services providers—the list of third parties that may have access to your network at any given time is lengthy. In fact, BeyondTrust research found that, on average, 182 vendors log into the systems of the.

Controlling the Risks of ThirdParty Access BeyondTrust
1. Consolidate third parties. First, you should identify everyone with a contract to provide services and catalog them in an authoritative system of record (SOR) that includes all user access.

Cognitas Use Cases ThirdParty Access
Fidelity is requiring these data aggregators to transition to this secure connection. Fidelity users of some third-party websites and apps may experience a disruption in the link between those websites and apps and their Fidelity accounts. However, there is no change to your ability to access your accounts or transact through the Fidelity app.

ThirdParty Access Governance Features Saviynt
Third-party access is rising in importance with several regulatory frameworks and is becoming a focal point for auditors. For example, Sarbanes-Oxley (SOX) includes several controls for managing third-party risk: APO10.01/APO10.02: Vendors must be selected per the organization's third-party vendor risk management policy and processes;

ThirdParty Access Control with Osirium PAM Osirium Blog
Search, Click, Done! Bringing an app store experience to IU services
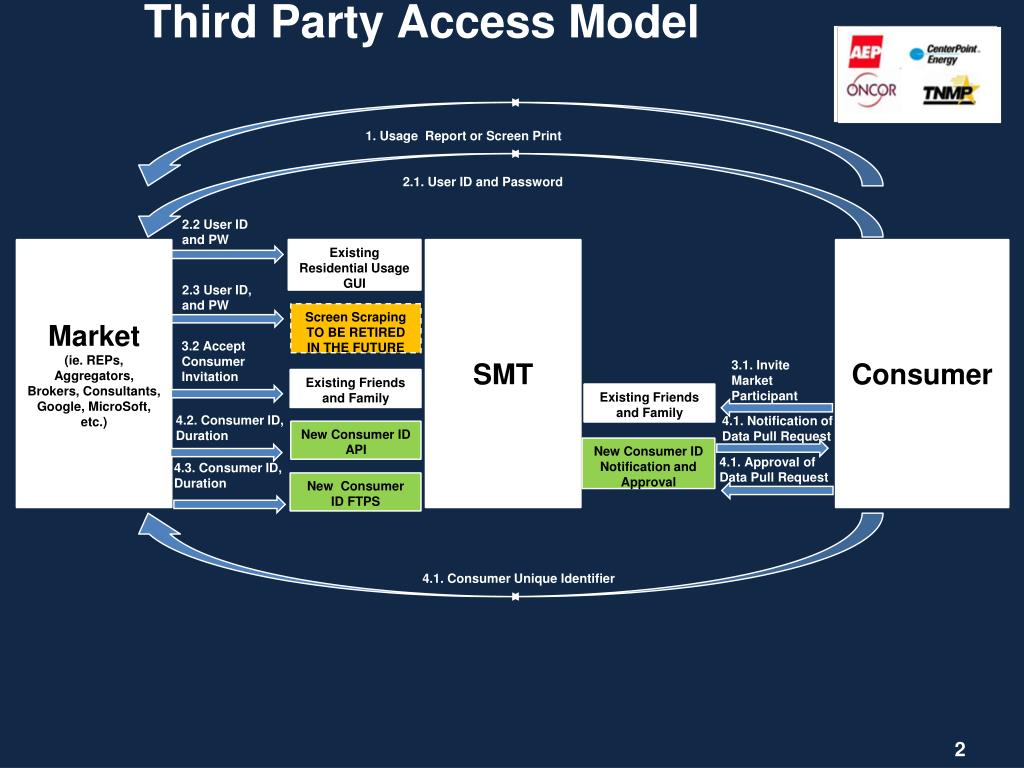
PPT SMT Model for Third Party Access PowerPoint Presentation, free download ID5503852
Tracking Protection limits cross-site tracking by restricting website access to third-party cookies. Google first revealed in 2021 its plan to get rid of third-party cookies, shortly after the European Union began investigating Google's advertising operations.. Competitors also have moved to block third-party cookies: Apple on Safari in 2020, and Mozilla on Firefox in 2019.

Third Party Access Accounts Receivable
Third-party vendor threats are pervasive. But they're not unconquerable. Being proactive and using these vendor remote access best practices can help mitigate the threat posed by third parties. Identify users. Audit all high-risk access points. Implement and enforce vendor remote access policies. Apply access controls.
Third Party Access • Definition Gabler Wirtschaftslexikon
Third-party access security involves managing and verifying vendor user identities, as well as implementing granular access control and authorization policies. Without such protocols, businesses are vulnerable to malicious attacks that can have serious financial, legal, and reputational implications. The recent spate of high-profile third-party.

ThirdParty Access Governance Features Saviynt
In a recent Ponemon Institute report on third-party remote access, 54% of responding organizations said they lack a comprehensive inventory of the third parties with access to their network.
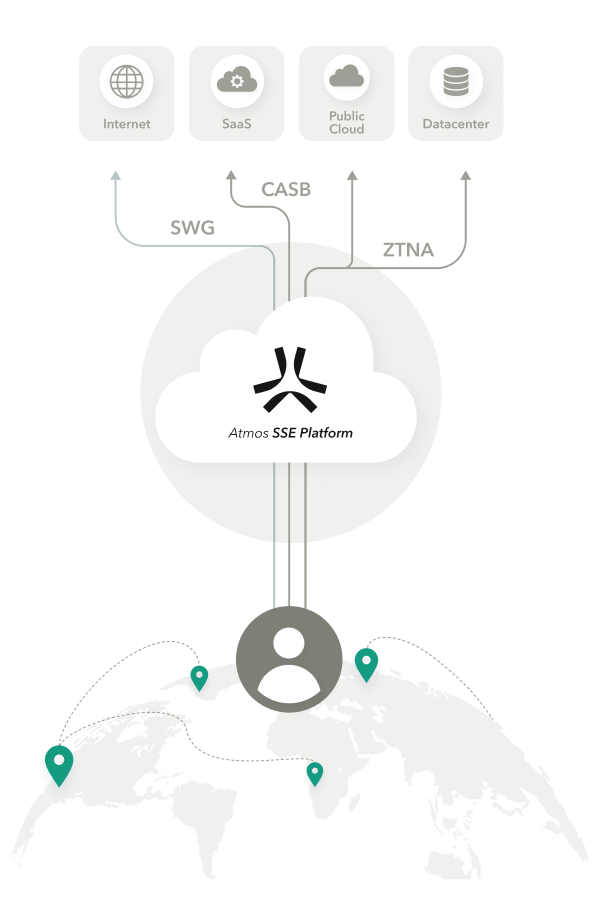
Secure ThirdParty Access & Least Privilege Access Axis Security
Google Chrome is restricting third-party cookie access for 1% of users as of January 4. Google expects to gradually ramp up the percentage of affected Chrome browsers, reaching 100% of users.

Third Party Access Policy IT Procedure Template
Secure access to your corporate applications without a VPN. Getting started with Access takes minutes. With our free plan, your first 50 users are free. Provide secure access to third-party contractors or partners with clientless ZTNA. Protect higher risk users and apps on your journey to Zero Trust.
Thirdparty access Use Cases Fyde
Third-party access use is worrying because recent data breaches have shown that it is a common factor in successful cyber-attacks. In January, co-working provider Regus suffered a highly-sensitive.

ThirdParty Access Risks Explained Authomize
To manage third-party access, click on one of the linked accounts to see a list of access features & restrictions. XYZ Company1 is expanded. Narrator: Here you can choose to stop linking this third-party service to individual accounts or disconnect it from all accounts. Additionally, clients can choose to opt out of automatically linking to new.
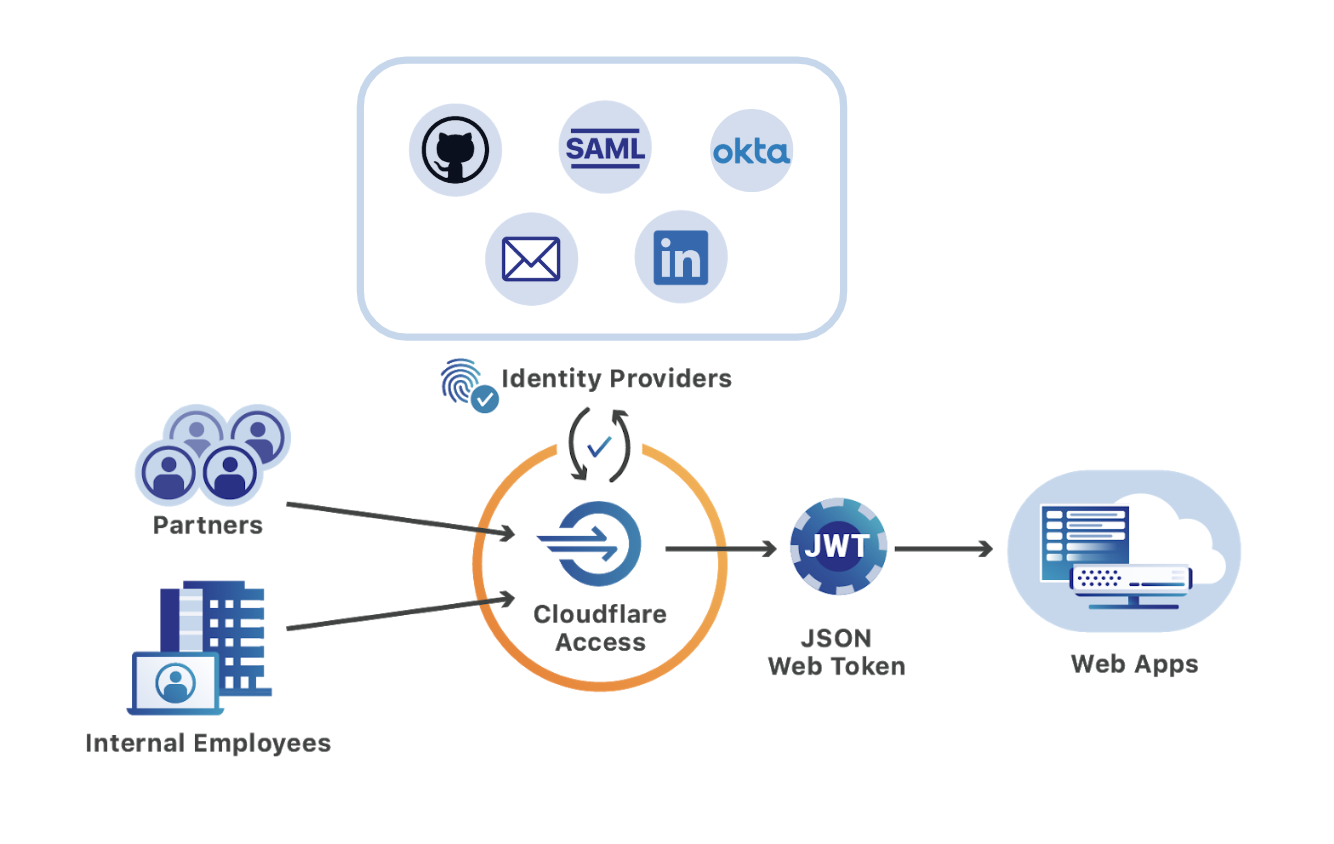
Third Party Access Cloudflare Zero Trust Cloudflare
7. Audit third-party access to ensure security. Regularly audit third-party access. Audits should check that access controls are functioning as designed. Check that third-party privileges are appropriate and that segmentation protects critical data. And routinely check for third-party suppliers that have escaped security controls.